It’s now easier than ever for cops to snoop on Americans without their knowledge.
Using technology known as pen registers and trap and trace devices, law enforcement can collect a wealth of data on internet and cell phone users, including who they call and email and what websites they visit. Through a federal law called the Stored Communications Act, police agencies can also force tech companies to hand over online communications records telling them all kinds of personal information.
All it takes to conduct electronic surveillance is a court order. Notably, pen register and trap and trace requests require a lower burden of proof than wiretaps, for which cops need a warrant. Rather than showing probable cause, police only need to demonstrate that the personal data they’re requesting is somehow relevant to a criminal investigation.
On top of that, under current court practices, it’s impossible to know how often judges grant electronic surveillance requests—much less how cops justify their surveillance, the forms of electronic surveillance permitted, and the companies compelled to assist with that surveillance. Federal court records related to electronic surveillance requests are filed under seal, and in many instances, they’re kept that way indefinitely. Even after police wrap up whatever criminal investigation they cited as a basis for their snooping.
Law enforcement conducts Internet and cell phone surveillance under complete secrecy, free from public scrutiny that could prevent them from abusing this power.
The Stranger filed a petition with the U.S. District Court for the Western District of Washington today asking the Court to publicly docket electronic surveillance cases and unseal certain applications and orders in those cases so they are accessible to the public. Additionally, we’ve asked the court to unseal surveillance orders dating back to 2011, covering a span of recent history that includes Occupy Seattle, Black Lives Matter, several May Day smashups, and the first year of the Trump administration.
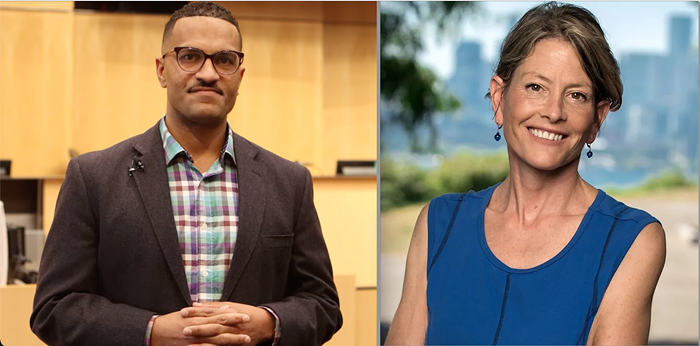
We’re represented by the Electronic Frontier Foundation, a nonprofit digital privacy and free speech advocacy group, and attorneys from the law firm of Dorsey and Whitney.
Our petition claims that the First Amendment and common law grants the public a right to access the requested electronic surveillance documents. As our lawyers write, public disclosure of these orders and applications “will further the public’s understanding of law enforcement, the Court, and the operation of the criminal justice system.”
We’re not the first organization to ask courts to unseal these types of surveillance orders. In D.C., the journalist Jason Leopold (then of Vice News, now of Buzzfeed) managed to free up information regarding thousands of surveillance orders from the federal district court in the U.S. capital. His petition, joined later by the Reporters Committee for the Freedom of the Press, revealed that police requests for electronic surveillance orders in the region increased 500 percent from 2011 to 2016. And in California, Riana Pfefferkorn of Stanford University and Jennifer Granick of the American Civil Liberties Union have been working on a similar effort to unseal surveillance records in the state’s Northern District.
Every court has its own method of keeping surveillance records under wraps. Back in July, I asked officials from the U.S. District Court for the Western District of Washington to walk me through how they manage non-warrant electronic surveillance cases. The Court’s Chief Deputy Clerk Lori Landis explained that such cases are designated as grand jury matters, even though they are not associated with any grand jury proceeding. As Landis explained to me, “We only use that case type so it can’t for sure be inadvertently unsealed.”
If our petition succeeds, the court will no longer use the grand jury designation for electronic surveillance cases, and information regarding those cases would show up on PACER, the online database for federal court documents. A favorable ruling would also free up more than five years-worth of records on electronic surveillance in Western Washington. At the very least, such records could tell us how often police ask the courts to authorize electronic surveillance in this district.
There are, of course, legitimate uses of surveillance to investigate criminal activity. There are also legitimate reasons to keep surveillance activity secret, particularly when revealing too much could compromise ongoing investigations. We understand if the government needs to redact some information from documents that are unsealed. But we believe that hiding surveillance records in their entirety—even when investigations conclude—flies in the face of transparency and the public’s right to access the judicial system.
The Stranger has a long track record of reporting on surveillance and police practices, from wireless mesh networks to social media tracking to Bureau of Alcohol, Tobacco, Firearms and Explosives cameras in the Central District. Records related to electronic surveillance at the federal level—particularly in this hub of tech and activism—could be a goldmine for stories in the same spirit.
We’re excited to share with you what we find out.